A recent report published by cybersecurity firm ESET has exposed a surveillance operation conducted by the China-affiliated advanced persistent threat (APT) hacking group known as GREF.
This hacking group had previously employed an Android malware tool named BadBazaar for spying on Uyghur populations, and it is now disseminating similar malware to individuals across multiple countries. This covert spyware campaign impersonates the popular messaging platforms Telegram and Signal in order to extract sensitive user data.
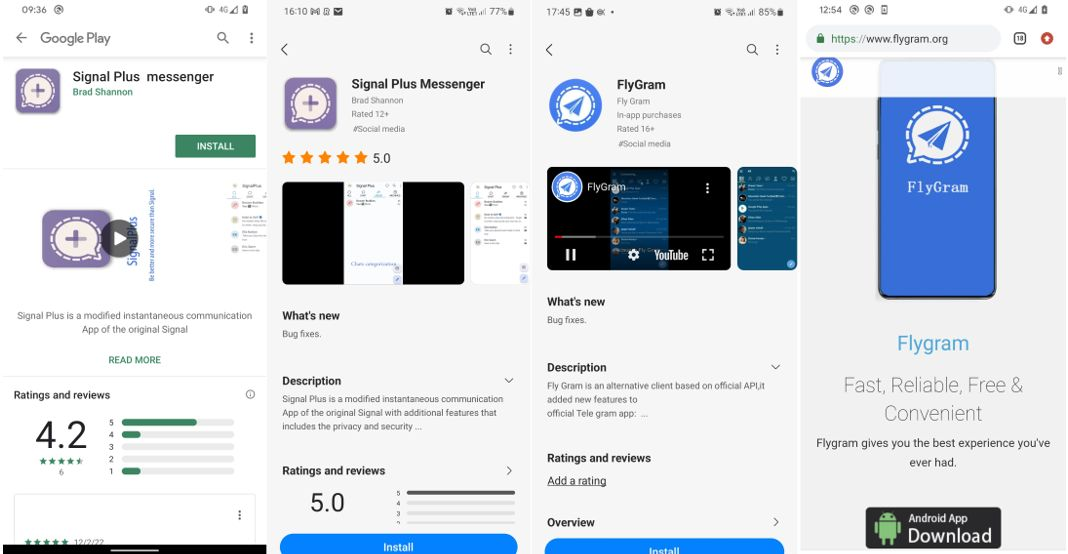
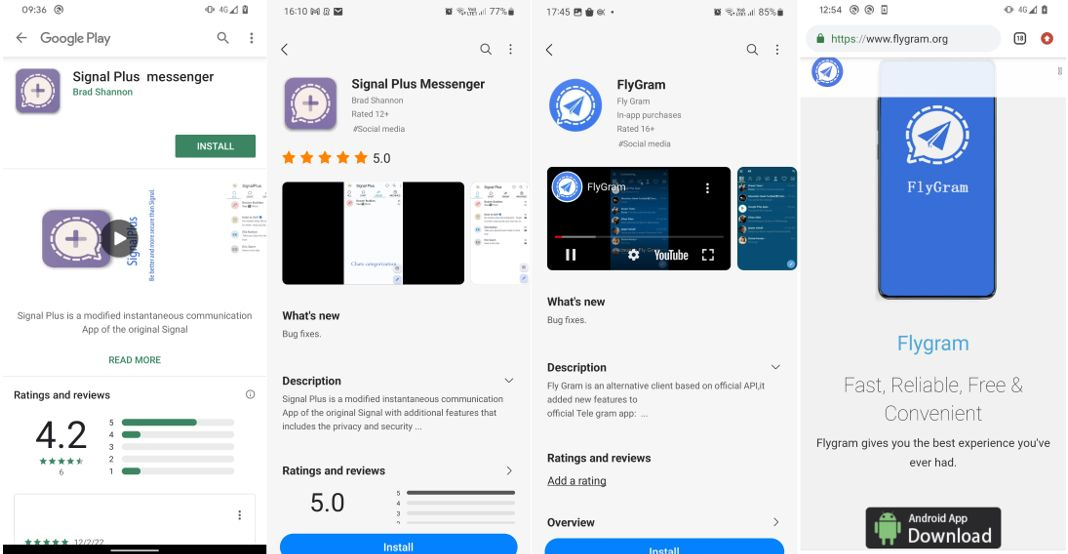
ESET discovered that malicious Android apps “Signal Plus Messenger and FlyGram” present on Google Play Store and Samsung Galaxy Store, were designed to infect the devices. These applications also had dedicated websites, impersonating the Signal application ( signalplus [.]org.) and Telegram alternative application ( flygram [.] org.)
The purpose of the spy app FlyGram and Signal Plus Messenger is to extract sensitive data of users, such as contacts list, call logs, list of Google accounts, device location and Wi-Fi information.
FlyGram has the capability to retrieve essential metadata from Telegram applications and gain access to a user’s complete Telegram backup, including contacts, profile pictures, groups, channels, and various other details, provided the user activates a Cloud Sync feature within the malicious application. Data related to the utilization of this specific backup feature indicates that a minimum of 13,953 individuals who downloaded FlyGram had it enabled, said ESET.
The main function of the Signal Plus Messenger is to spy on user’s Signal messages. The malware extracts the user’s Signal PIN and utilizes it to establish connections between Signal Desktop and Signal iPad with the attacker’s mobile devices.
The video presented by the researcher demonstrates the threat actor’s ability to establish a connection between the compromised device and the attacker’s Signal account seamlessly, all without requiring any action from the user. Additionally, it provides instructions on how users can verify if their Signal account has been linked to another device.
FlyGram, uploaded to Google Play in June 2020, garnered over 5,000 installations before removal in January 2021.Signal Plus Messenger, uploaded on July 7th, 2022, received over a hundred installations before being taken down in May 2023.In addition to these distribution channels, it is noteworthy that potential victims may have been deceived into installing the applications through participation in a Uyghur Telegram group dedicated to Android app sharing. This group boasts a membership of over 1,300 individuals.
According to the report victims have primarily surfaced in Germany, Poland, and the United States, with additional cases identified in Ukraine, Australia, Brazil, Denmark, Congo-Kinshasa, Hong Kong, Hungary, Lithuania, the Netherlands, Portugal, Singapore, Spain, and Yemen.
Chinese Surveillance Operation
Cybersecurity firm “Lookout” has identified BadBazaar as a surveillance tool employed by the Chinese government in surveillance campaigns targeting Uyghurs and other Turkic minorities, both within China and beyond its borders.
According to ESET, there are significant code similarities between the Signal Plus Messenger and FlyGram samples and the BadBazaar malware family, attributed by “Lookout” to the GREF cluster of APT15. There is also overlap in the targeting, with the malicious FlyGram app using a Uyghur Telegram group as one of its distribution mechanisms. This aligns with the targeting of other Android malware previously employed by GREF.
ESET warned of this to both Google and Samsung, which resulted in the removal of both apps from Google platforms. However, there has been no action reported by Samsung.